OS X Security Tips

Besides growing speculations about Mac’s inbuilt security and the advent of various malware that were once non-existent on Apple’s computers, Mac OS X is still a respectably stable and secure operating system. While Apple tries its best in protecting you from viruses and other internet hazards, there are certain security elements that are just not in the vicinity of the operating system. Most of the time users tend to overlook these by trusting the OS more than its really capable of.
The Basics:
Mac users should take some precautions and these are pretty straightforward. These include staying away from spam and phishing emails, disabling auto-login, creating strong passwords using password managers. In addition, installing applications only from trusted sources is also a good idea. And the most important of all is to keep your operating system and applications up to date. Other than that, Mac users who want to stay secure should follow the
Use a non-admin account for everyday tasks and disable auto-login:
Once you unbox a newly ordered Mac and proceed with setting it up, the first thing your device will ask you to do is set up a username and a password. This information is used to set up your initial user account. By default, the first user account is always the one with administrative rights and is known as the administrator account. This is where you would be able to install all your system files and perform various other unrestricted tasks. While an administrator account allows its owner to do almost everything he or she requires, the more often you use it, the more you are exposed to risks.
For common everyday tasks like surfing the web, watching a movie or listening to your favourite music, there is a much simpler and safer alternative – creating a standard account. Since standard users have limited rights, even if they make certain mistakes, they wouldn’t have to worry about the safety of their device.
Security and Privacy settings:
One of the first things to pay attention to after setting up your account is security and privacy settings. To access them, you’ll find a padlock at the bottom of the screen. Once you click it, it will ask you for your username and password. While there isn’t any perfect configuration, be cautious and set up the computer’s privacy according to your needs and preference.
Turn on firewall
Probably almost all of us have heard or read the word ‘firewall’ and that too not just once, though, only a few actually know what purpose it serves. Its function is simple and straightforward. It keeps you safe by blocking all unwanted internet connections while you are online. You might consider it to be enabled by default, however, it often isn’t.
Fortunately, it is pretty quick and easy to do that. While in the Security and Privacy settings we discussed earlier, click the Firewall tab in the system preferences. Locate the padlock on the bottom left side of the unlock system settings and click the button that says Turn on Firewall.
Use password managers:
While creating a strong and secure password is essential, the more complex they are, the easier it is to forget. Wouldn’t it be great if we had someone to constantly remind us of them? Well, there is good news! Password managers have made a lot of positive headlines lately and for sure, there is a big reason to love them, including not having to remember so many different, unique, complex passwords! Some of the most highly rated applications capable of storing passwords for the Mac OS X are LastPass and DataVault.
Use a VPN
You probably wouldn’t have to worry about using a VPN while you are online unless you have a habit of connecting to your neighbor’s Wi-Fi. However, if you are out with your MacBook and the only way of accessing the internet is through public Wi-Fi, consider using a VPN software. VPNs protect you from culprits trying to sniff data from people connected to the same network. This data may even include credit card numbers.
Avoid piracy
Installing illegal software might expose your information to a malware that might come along on the back of it. Even though OS X has always been the best at its game when it comes to defending the device from dangerous threats, it isn’t completely immune. Sticking to trusted sources for installing applications is the right way to go.
Additionally, most pirated software are shared through peer-to-peer platforms, which expose your information to everyone on the network, leading to potential unpleasant consequences.
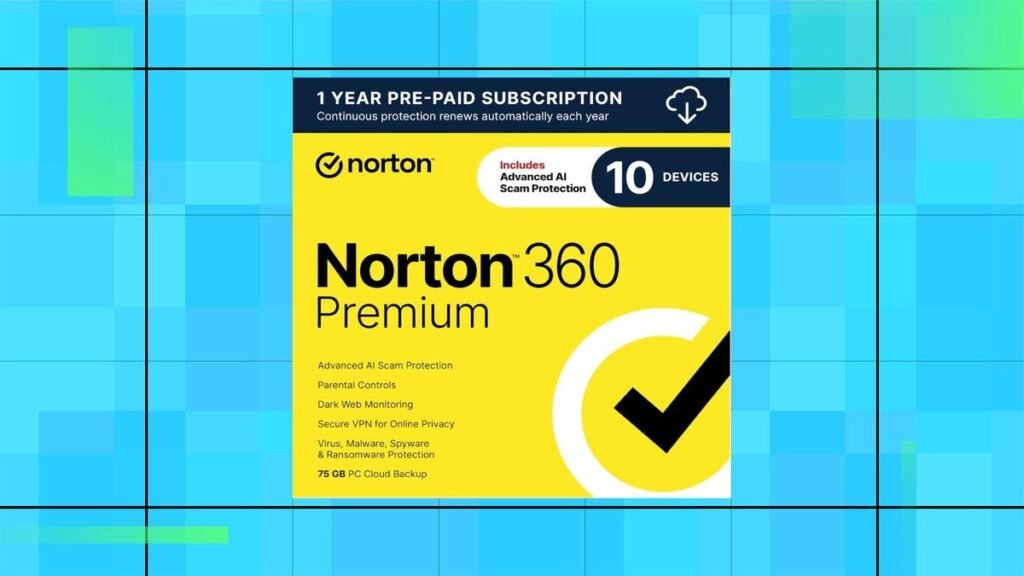
Use antivirus
As mentioned earlier, a Mac doesn’t really require an antivirus as much as a Windows PC or laptop does. OS X is much more stable and secure than it is being speculated or criticized nowadays. However, there have been a good number of cases of the system being affected by malware and the numbers are still increasing.
Though, a home user wouldn’t require an antivirus as much as a business owner would, having one installed wouldn’t hurt. For more insight on this subject check out our article – Do I need an antivirus for OS X?
Keep your computer safe and install a tracker app
Last but not the least, never leave your MacBook unlocked or unattended. Macintosh laptops are expensive and are potential targets of thefts. Leaving them unlocked, might have daunting consequences.
Losing a MacBook is more than frustrating, having information exposed to the wrong people is a lot more distressing. Installing a tracker app might not necessarily get you your device back, however, it would certainly protect your data from reaching the wrong hands.
OS X Security Tips conclusion
Following the tips in this article should protect users from a wide range of potential OS X security threats. Browse rest of our articles for more advice on how to secure yourself online, from social media to your smartphone devices.
Be the first to write a comment.